
1. Nature and types of threat
A threat is anything that, after gathering information from a range of sources, is seen to have the possibility of interfering, discontinuing, or even destroying a given service, a specific asset or also adversely affecting operations. Threat is formulated as capability x intent, where intent indicates the intentionality, tacit or declared, to cause an offense, and capability denotes the aggressor’s ability to possess the physical means to carry it out. The aspects of opportunity and motivation should also be investigated, as different people have various degrees of motivation and various opportunities to execute some threats.
Once detected, threats must be contextualized in relation to the environment within which they exist. A wide range of scenarios arises from natural and artificial hazards that could be classified into:
External hazards (i.e., violent acts, civil disorders, terrorism, and criminal activities),
Internal hazards (i.e., internal theft and sabotage),
Natural or meteorological hazards (i.e., hurricanes, severe storms, cyclones, floods, drought, earthquakes, volcanic activity, wildfires, tsunamis),
Environmental hazards (i.e., water stress and heat stress),
Workplace accidents (i.e., structural collapse, mechanical breakdown),
Chemical, biological, and radiological accidents,
Transportation interruptions (i.e., significant road closure, widespread flight delays),
Information technology and communication interruption.
To evaluate in which degree and probability threats will become a reality, threat assessments are conducted considering the following classification:
Actual threats, based on historical records or the location of the assets,
Inherent threats, due to the nature or characteristics of the facility or the operation, and
Potential threats, which exist by virtue of vulnerabilities around the asset or weaknesses in the security program.
2. What is a Threat Assessment?
Threat assessment has different meanings depending on the person who is using it. Security professionals, police, judges, and psychologists conduct threat assessments, but using different approaches. Each approach is predictive in nature, however their differ for the methodology used. In the security field, threat assessment is therefore defined as the approach that utilizes several strategies or methods to prioritize the seriousness, identify and evaluate potential or imminent threats to prevent or mitigate the possibility that they will be performed. For people working in the security industry, threat assessments are the first step in risk and vulnerability analysis.
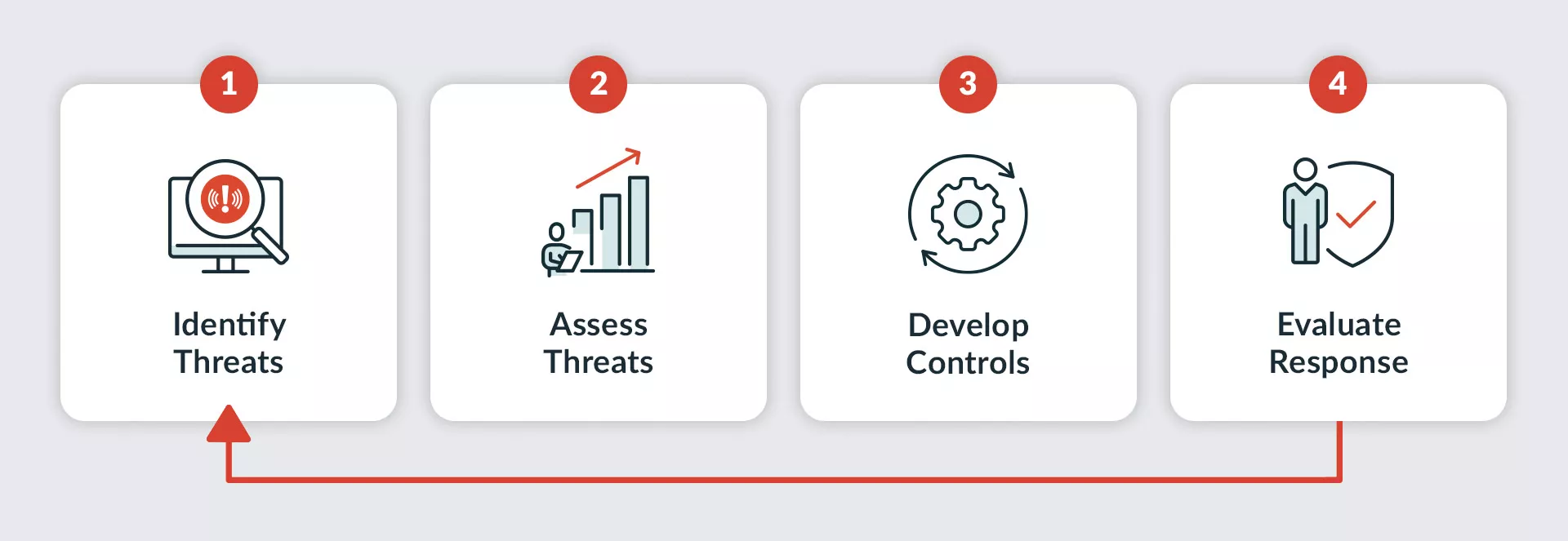
The assessment is composed of four main steps that include threat identification, an initial assessment to determine the seriousness of the threat (this step sees the involvement of different sources, both at the level of HUMINT and through the analysis of social media channels), case management where a short-term or long-term intervention plan is developed and, lastly, the follow-up, which entails a constant analysis of the R-S-I-F- indicators, the threat recency, severity, intensity, and frequency by the threatener.
Once threats are identified and analyzed, entities can decide how to protect the assets at stake. While performing a threat assessment, it is fundamental to involve external stakeholders and partners, as they may play a pivotal role in the emergency response efforts, such as local law enforcement officials, ad hoc and mental health professionals.
The term active threat assessment is also used and refers to the systematic observation of behaviours and actions aimed at identifying threats. In this methodology, an observer (generally the security or the intelligence officer) systematically monitors the environment, detects suspicious individuals (also known as persons of interest - POI), and assesses the potential threats these individuals pose. A POI is an individual who, identified from information and referral, is a target for additional observation due to suspicious activity or threatening behaviour. The use of indicators helps pinpoint if the individual might represent a threat.
The concept of threat goes inevitably hand in hand with that of vulnerability.
3. Vulnerability analysis
Let us take the example of national defence. A country is constantly under different threats; the gaps in the national security system are the vulnerabilities, and the potential damage to the assets or the citizens, are the risks. A vulnerability is defined as a weakness in an environment that can be exploited to deliver a successful attack.
Therefore, the threat assessment is followed by the vulnerability assessment, which comprises two parts. The first involves the determination of the assets (i.e., people, properties, equipment) and the loss estimation in case of a successful attack. The second is an assessment of the target’s attractiveness level and the existing defense mechanisms against each threat.
The purpose of vulnerability analysis is to evaluate what was identified in the gathering of information and determine the current weaknesses, and establish if the safeguards in place are adequate in terms of confidentiality, integrity, or availability. Threats will always exist; however, if there are no vulnerabilities, there will be low chances of risk. Hence, knowing about common vulnerabilities and tracking them regularly is fundamental to detecting potential risks.
4. The notion of “risk”
Threats are evaluated based on the assessment of their risk. Risk is calculated as a function of the likelihood or chance of occurrence of a particular set of circumstances (from most unlikely to most likely) and impact, the magnitude of consequences if the event occurs in the absence of action and controls. Risk can also be defined as the effect of uncertainty on objectives, where uncertainty means not knowing how or if potential events may manifest, and the impact will be the consequences or outcome of the event affecting objectives.
Each risk assessed must be considered based on the likelihood of occurrence to which a threat may take advantage of a weakness, the potential adverse impact that would result, and a recognition of what this situation could mean. For each risk that is identified, a planned action must be taken.
There are different ways to analyze risk, and it is challenging to identify and implement effective models that objectively assess the probability of loss based on current threats. Without a substantial measurement strategy, make confident decisions and forecast future resource allocation and security investments is hard. Once the right metrics are found, the next step is to search for the tools needed to measure those metrics and build the correct narrative to efficiently convey the findings to decision-makers. Making the appropriate decisions requires weighted considerations, investigating the potential benefits and implications, and finding a balance between them. The analyst must be able to collect information and data from several methods and therefore combine all the pieces to be able to create an extensive plan for security management while assessing compliance with customary practices and applicable laws. The more detailed and specific the analysis is, the more clarity we have on dealing with the risks.
Nowadays risk management has become a real discipline, which aims to understand how to prevent possible harmful events, what to do in such cases and how to mitigate their potential consequences, with the view to preserving business continuity. The evolution of best practices has led to the development of specific norms, standards and frameworks based on research and experience accumulated over time. The International Organization for Standardization (ISO) has codified the 31000 as a family of standards related to risk management, which seeks to provide a universally recognized paradigm for professionals and companies employing risk management processes.
5. The role of Key Risk indicators
A key risk indicator (KRI) is a metric for measuring the likelihood that the probability of an event and its consequences will exceed the risk threshold and impact an asset profoundly. They help measure, monitor, and control the tools, the implemented strategies, and the weaknesses. A good KRI should be:
Measurable: quantifiable in numbers or percentage
Predictable: provide early signals of risks
Comparable: follow a scale for comparison
Informational: provide an accurate view of the risk status.
Its primary role is to facilitate the identification of risks, threats, and vulnerabilities the entity faces based on their likelihood of occurring, their operational and financial impact, and the ability to mitigate such events. They rank its features in terms of criticality and potential harm; in this way, the risks of most significant concern are identified as when and how they become a severe threat.
KRIs are thus the red flags that ensure the risks are spotted in advance and mitigated. They must be regularly monitored and reviewed to check for any possible situational change, and any risk or threat levels modifications and initiate remedial action that may be required as a result.
The major challenges associated with developing KRIs are generally linked with obtaining accurate information that can be used to pinpoint critical activities. Also, once risks, threats, and vulnerabilities are identified, they should be quantified by likelihood, severity, and impact. The critical event must be realistically linked to the most likely risk scenarios. Lastly, it is essential to create measurable and understandable metrics to be able to establish remediation if deviations to KRI metrics occur.
6. Risk assessment
Once the threats are identified, a way to evaluate the impact and likelihood of those threats should be found. These further assessments will determine the overall risk level. Nowadays, many techniques are used to conduct risk assessments, but only a few are open-source and available for free.
A risk assessment is a systematic process aimed at evaluating a potential risk while identifying actions to prevent, mitigate, and, in case, recover through the application of ad hoc regulations and supplementary measures. It collects all the essential information, displays the weak spots, provides the tools to evaluate the consequences of potential security incidents, and helps improve security practices and prevent incidents. It mainly consists of the following steps:
Risk identification: while determining the risks that could mostly threaten an asset or the society, a risk matrix, also called a probability matrix or impact matrix, can help assess the level of each risk and facilitate the assessment through an estimation of the likelihood that the threat will occur and the potential impact the threat will have on the assets. The harm severity (or impact), put in the framework’s horizontal axis, has five levels of categorization: from insignificant to severe. The vertical axis analyses the probability (or likelihood) of the harm occurring and is ranked on a five-point scale as well, ranging from rare to almost certain.

The criticality of the threat, the relevance of the assets at risk, the probability of occurrence, and vulnerabilities must be considered as they influence the likelihood of a threat occurring. In addition, it is important to consider also other factors such as the location of a resource and historical events. Three are the main broad categories that can be impacted by a threat: people, locations, and assets.
Risk analysis: It aims at studying the existing and necessary countermeasures and revealing opportunities for their upgrading or improving. If we take as an example an airport terminal, a potential threat can range from natural disasters to organized criminal attacks, or just accidents (i.e., a computer failure causing the shutting down of the whole communication system). Each of these threats will require different response approaches. In the case of a large airport in a metropolitan city without nearby airports, any suspension of services would create significant disruption. In contrast, a small country airport would have a reduced effect. By considering the attractivity factor, a small airport may be a less attractive target.
Risk evaluation: Once rated the risks based on likelihood and impact, and reviewed the adequacy of the measures in place and their desired effect when designed and implemented, the residual risk is obtained, meaning the remaining risk levels after considering the effectiveness of the mitigation measures. Defining risk appetite and comparing it with the residual risk helps determine whether the risk is acceptable or requires additional actions. As soon as the potential threats have been identified, the impact assessed, and the measures developed, it is time to evaluate the response. This means examine all implemented countermeasures that would mitigate the threats.
Risk communication: At this point, once the adequate assessments have been carried out, the findings are shared with the relevant stakeholders: risk assessors, risk managers, ad hoc businesses, and the scientific community. By consulting all the involved parties, alternative interventions are examined. Risk communication is the basis for risk management decisions, and involves an interactive exchange of points of view, perceptions, data, and information regarding hazard elements, risk factors, and explanations of risk assessment outcomes. Creating a comprehensive report will help convey the risk-related information, simplify the decision-making processes, and improve the whole risk management approach.

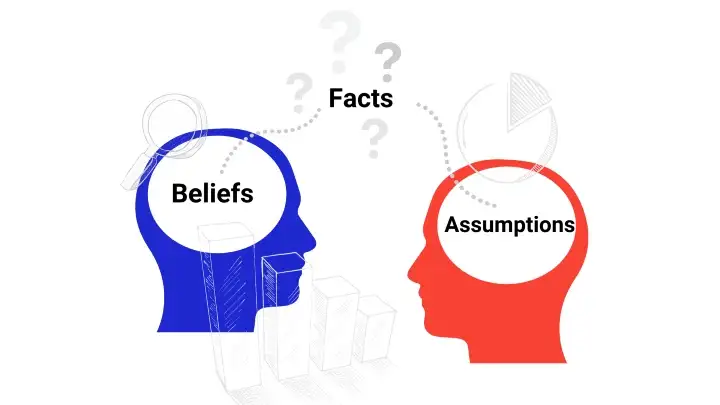
7. Cognitive bias
While measuring the risk, several cognitive biases can cause poor judgment of the likelihood of something happening, either the overestimation of the risks, without adequately considering the consequences of the actions. Cognitive biases are systematic errors in thought that impact the decisions people make. These biases derive from experiences, aptitudes, and perceptions, and are often influenced by other factors, such as fears. Several different biases emerge at every stage of the risk assessment process that could lead to unreliable outcomes that directly impact the decision-making. For this reason, it is fundamental to utilise the proper techniques and strategies to help mitigate or eliminate biases.
However, it is nearly impossible to completely eliminate them. Overcoming these impulses requires the realization of an effective framework that can be consistently improved over time. To mitigate bias is firstly essential to recognize that biases exist and then implement strategies to neutralize them. Some best practices should be considered to guarantee a more objective risk analysis and improve decision-making processes, ensuring that the perspectives are always balanced, and the insights are varied. An added value could be considering both internal and external perspectives (i.e., consultants, experts, and analysts), as having different opinions from different groups can better help identify the objectives and biases.
8. Conclusions
Threat and risk assessments detect exposures by spotting potential security weaknesses and searching the appropriate actions to reduce the impact of threatening events and manage the risks. The outcome of these assessments is to provide recommendations that adequately address the security standards, the protection of confidentiality, integrity, and availability, while still providing efficiency and usage of the involved assets.
This can be accomplished using either internal or external resources. The choice will depend on the situation and mainly on the urgency of the actions that must be taken. It is crucial that these processes are collaborative in nature, as without the involvement of the various levels and stakeholders, the assessments could lead to costly and ineffective security measures. The threat and risk assessment are not a tool to an end. They are a continuous process that should be reviewed on a regular basis to ensure that the protection mechanisms currently in place still meet the required objectives.
(download the analysis)
Bibliography
Botha, A. (2021). Chapter 28: Prevention of Terrorist Attacks on Critical Infrastructure. In the Handbook of Terrorism Prevention and Preparedness.
Cybersecurity and Infrastructure Security Agency (CISA). (2019). A Guide to Critical Infrastructure Security and Resilience.
Simons, A., & Meloy, J. R. (2017). Foundations of threat assessment and management. In The Handbook of Behavioral Criminology, 627-644.
Serin, R.C., Lowenkamp, C.T., Johnson, J.L., & Trevino, P. (2016). Using a multi-level risk assessment to inform case planning and risk management: Implications for officers. Federal Probation, 80, 10.
